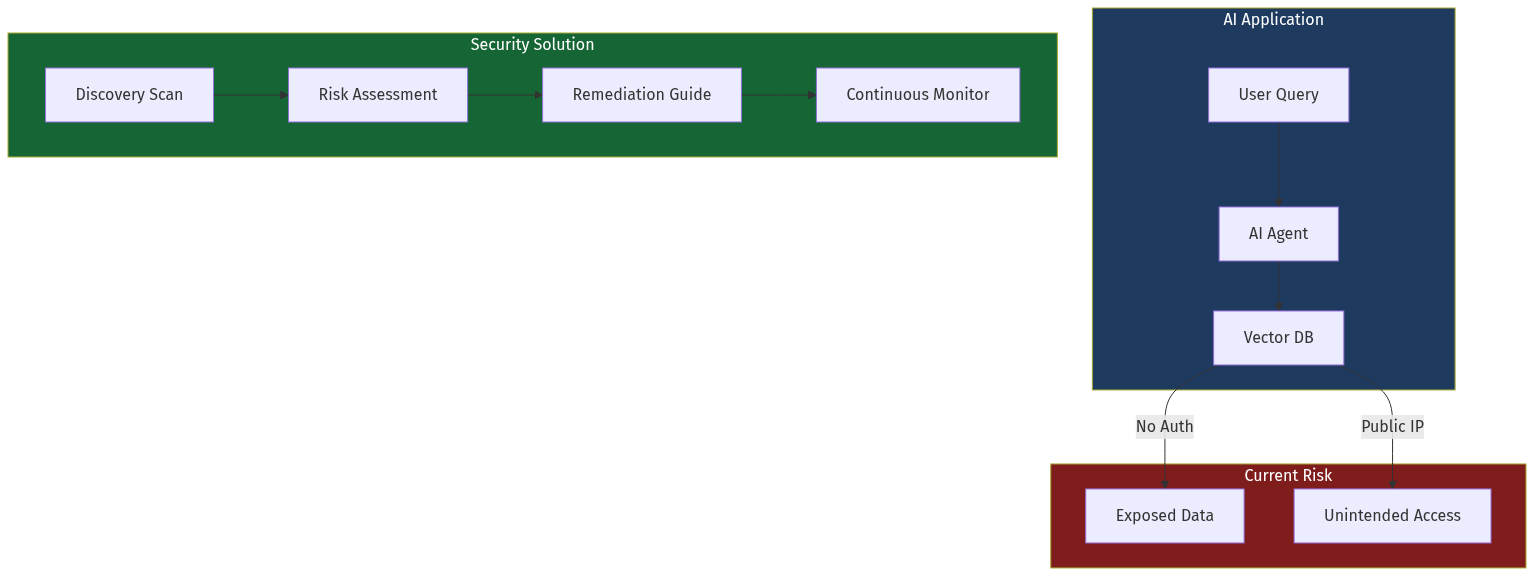
A recent security scan revealed that thousands of Vector databases — the critical infrastructure powering AI applications — are publicly exposed without authentication. This represents both a massive security risk and a compelling B2B opportunity.
The AI application market is growing at 40%+ CAGR, but security infrastructure has not kept pace. Enterprises adopting AI need purpose-built security solutions that understand the unique architecture of Vector databases, RAG pipelines, and AI agent workflows.